Embark on a journey through the labyrinthine world of onion links. These enigmatic pathways, often shrouded in layers of obfuscation, lead to hidden destinations and untold information. With each click, you penetrate another layer, gradually revealing the true nature of the connection. Onion links harness sophisticated cryptography to ensure anonymity and security, making them a coveted tool for those seeking privacy and protection. However, navigating this intricate network necessitates caution and awareness.
- Deciphering the strata of onion links can be a tricky task, needing specialized tools and expertise.
- Beware of potential risks lurking within the onion network, as malicious actors may attempt to manipulate unsuspecting users.
Venturing into the Dark Web: A Guide to Onion Links
Diving deep through the oniony depths of the dark web can feel like launching on a perilous journey. But armed with knowledge, you can confidently navigate its labyrinthine paths. The key? Understanding onion links - those cryptic addresses that act as gateways to hidden realms.
Onion links, frequently known as .onion addresses, are unique identifiers for websites hosted on the Tor network. Unlike traditional URLs, they utilize multiple layers of encryption, making them difficult to trace and giving users a higher degree of anonymity.
- To access these hidden sites, you'll need a specialized browser like Tor. Once installed, simply paste the onion link into the address bar and hit enter. A new window will load, revealing the content of the website.
- Remember, care is paramount when browsing the dark web. Be wary of phishing attempts and never share sensitive information unless you are absolutely certain of the site's legitimacy.
Exploring the dark web can be a fascinating experience, offering access to a world of hidden knowledge and alternative viewpoints. But it's essential to remember that with great power comes great responsibility. By understanding the risks and taking appropriate precautions, you can securely explore this enigmatic territory.
Unveiling the Veil: Onion Services and Their Potential
Onion services, also known as Tor hidden services, represent a intriguing realm within the virtual landscape. These private networks operate through a series of encrypted layers, effectively concealing the identities of both users and websites. This layered approach masks the true origin and destination of information, making it challenging to trace online activity.
- Onion services provide a platform for private communication, safeguarding users from surveillance and censorship.
- Furthermore, they enable access to information that may be censored in certain regions or by governments.
- On the other hand, the secrecy offered by onion services can also be misused for illicit activities.
The challenges surrounding onion services are complex and multifaceted, sparking ongoing discussion. Nevertheless, their potential to enable individuals and facilitate freedom of expression remains a compelling driving factor in the ever-evolving online world.
Privacy on the Web: Onion Links Explained
In the digital realm where data is constantly being tracked, private browsing has become paramount. Onion links, a cornerstone of the Tor network, provide a layer of protection that empowers users to navigate the web with greater privacy. By routing your connection through multiple servers, onionlinks onion links obscure your IP address, making it very difficult for trackers to follow your online actions.
- Leveraging onion links offers a valuable tool for citizens who value their anonymity.
- From utilizing restricted information to defending your personal details, onion links have a wide range of uses.
Therefore, understanding the relevance of onion links is crucial in today's digital landscape, where privacy is increasingly desired.
Delving into Onion Links Safely
Onion links, also deep web gateways, can offer a tantalizing glimpse into obscure corners of the internet. While they provide access to information that's rarely accessible through traditional means, it's vital to approach them with care. The allure of the unknown can be compelling, but the risks connected to onion links should never be overlooked.
- Existing dangers include vulnerability to malware, scams, and illegal activities.
- Furthermore, anonymity provided by onion links can be exploited for malicious purposes.
- Consequently, it's imperative to utilize robust security measures, such as strong passwords, reputable antivirus software, and vigilance when interacting with onion link content.
By mindfully considering the risks and rewards, you can explore the world of onion links ethically.
Unlocking the Mysteries of Onion URLs: A Guide to Navigating the Dark Web
Deep within the labyrinthine corridors of the internet, a clandestine realm operates shrouded in anonymity. This hidden world, known as the Onion Network, relies on a unique form of address—the onion URL. These enigmatic links appear as a jumble of seemingly random characters, often preceded by "onion" or "tor." Decoding these cryptic sequences unveils a world where users can communicate and share information with unparalleled anonymity. The TorBrowser, the driving force behind this hidden network, utilizes layers of encryption to obscure user identities and browsing history. To access the Onion Network, one must use specialized software like the Tor Browser. This program guides users through a complex web of relays, effectively encrypting their traffic and rendering their location undetectable.
- Individual onion URL represents a unique website or service. These sites often provide access to information that is restricted in the open web.
- Visitors on the Onion Network can interact with each other and share data without fear of monitoring.
- This hidden nature of onion URLs makes them a popular choice for whistleblowers, activists, and journalists seeking to protect their anonymity.
While the Onion Network offers valuable benefits, it's important to approach it with caution. The anonymity provided can also attract malicious actors, making it essential to practice safe browsing habits and use trusted sources.
 Edward Furlong Then & Now!
Edward Furlong Then & Now! Katie Holmes Then & Now!
Katie Holmes Then & Now! Elisabeth Shue Then & Now!
Elisabeth Shue Then & Now!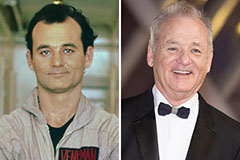 Bill Murray Then & Now!
Bill Murray Then & Now! Peter Billingsley Then & Now!
Peter Billingsley Then & Now!